IDS/IPS – Security and Compliance 1 – Cloud Perspective
Cloud Exams, Cloud security tools and technologies, Data loss and recovery, Exams of CloudIDS/IPS
IDS and IPS are essential components of a comprehensive cloud security strategy. These systems are designed to monitor network traffic and detect potential security threats and intrusions in real time. IDS focuses on identifying suspicious activities, while IPS goes a step further by actively blocking or mitigating threats. Let’s delve into the details of IDS/IPS in the cloud, along with some of the tools and services available for effective intrusion detection and prevention:
- IDS:
- Signature-based detection: IDS uses a database of known attack signatures to identify malicious patterns in network traffic. When traffic matches a signature, IDS generates an alert for further investigation.
- Anomaly-based detection: Anomaly-based IDS looks for deviations from normal network behavior. It establishes a baseline of typical network activity and raises alerts when traffic patterns deviate significantly from the norm.
- Network traffic analysis: IDS inspects packets traversing the network, analyzing headers, payloads, and patterns to identify potential threats such as port scans, buffer overflows, or other suspicious activities.
Figure 6.6 depicts an example of IDS/IPS placement in an environment:
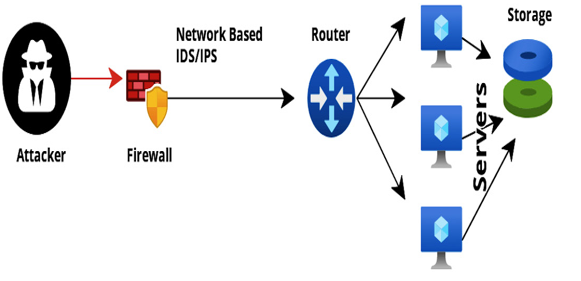
Figure 6.6 – IDS/IPS in an environment
- IPS:
- Real-time blocking: IPS not only detects intrusions such as IDS but can actively respond to threats. It can block malicious traffic or take preventive actions, such as resetting connections or sending alarms.
- Automatic response: IPS can trigger automatic responses based on predefined rules, such as blocking IP addresses or dropping packets from suspected malicious sources.
Now, let’s look at some IDS/IPS tools and services:
- AWS GuardDuty: AWS GuardDuty is a managed threat detection service that continuously monitors AWS accounts for malicious activities, unauthorized behavior, and potential security threats.
Setting up AWS GuardDuty is a straightforward process that involves a few simple steps. AWS GuardDuty is a managed threat detection service that continuously monitors AWS accounts for malicious activities, unauthorized behavior, and potential security threats. Here’s a step-by-step guide on how to set up AWS GuardDuty:
I. Access the AWS Management Console: Sign in to your AWS account using your root credentials or an IAM user with administrative privileges. Then, access the AWS Management Console.
II. Navigate to AWS GuardDuty: In the AWS Management Console, navigate to the GuardDuty service by either searching for GuardDuty in the search bar or finding it under the Security, Identity, & Compliance section.
III. Enable GuardDuty for your AWS region: In the GuardDuty dashboard, click on the Get Started button. You will be prompted to enable GuardDuty for the AWS region in which you are currently working.
IV. Choose a detector name: Enter a name for your GuardDuty detector. The detector is a logical entity that represents your GuardDuty setup in a specific AWS region.
V. Enable CloudTrail (optional): If you already have AWS CloudTrail enabled, you can choose to enable CloudTrail data ingestion for GuardDuty. CloudTrail logs provide additional context for threat analysis.
VI. Enable VPC Flow Logs (optional): If you have VPC Flow Logs enabled in your AWS environment, you can choose to enable VPC Flow Logs data ingestion for GuardDuty. VPC Flow Logs provides network traffic visibility for analysis.
VII. Review your settings and create the detector: Review your settings, such as CloudTrail and VPC Flow Logs, and click on the Create button to create the GuardDuty detector.
VIII. Wait for detector activation: After creating the detector, GuardDuty will start analyzing the AWS CloudTrail logs and VPC flow logs (if enabled) for potential threats. The activation process may take a few minutes to complete.
IX. Review and act on your findings: Once GuardDuty is activated, it starts generating findings based on its analysis. You can view these findings in the GuardDuty dashboard, along with details about the severity of the findings, affected resources, and recommended actions.
X. Configure notifications and remediation (optional): Optionally, you can configure CloudWatch Events to send notifications based on GuardDuty findings. You can also set up automated remediation actions through AWS Lambda based on specific findings.
XI. Monitor GuardDuty regularly: Regularly monitor the GuardDuty dashboard to stay aware of potential security threats and take appropriate actions to address them.