DoS attacks – Security and Compliance 1 – Cloud Perspective
Cloud Exams, Cloud security tools and technologies, Data loss and recovery, Exams of Cloud, Performance optimization, Subnetting and IP addressingDoS attacks
Cloud services can become targets of DoS attacks, which aim to overwhelm resources and disrupt service availability. Understanding DoS attack risks will lead us to explore strategies for the detection, mitigation, and prevention of such attacks.
DoS attacks are malicious attempts to disrupt the normal operation of an online service, network, or cloud environment by overwhelming it with a massive volume of traffic or resource requests. The primary objective of a DoS attack is to render the target inaccessible to legitimate users, causing service downtime and disruption. These attacks can have severe consequences for businesses and organizations, leading to financial losses, damage to reputation, and loss of customer trust. Understanding the intricacies of DoS attacks is essential for implementing effective mitigation strategies and ensuring the resilience of cloud-based systems.
Types of DoS attacks
There are different types of DoS attacks:
- Volume-based attacks: These attacks flood the target with a high volume of traffic, consuming network bandwidth and overwhelming server resources
- Protocol-based attacks: These attacks exploit weaknesses in network protocols to consume server resources, leading to service degradation or unresponsiveness
- Application layer attacks: Also known as Layer 7 attacks, these target specific applications or services, such as web servers, by exploiting vulnerabilities and causing them to become unresponsive
- Distributed denial-of-service (DDoS) attacks: DDoS attacks involve multiple sources to coordinate and launch the attack simultaneously, making it more challenging to mitigate
The impact of DoS attacks
DoS attacks can have severe consequences:
- Service disruption: The primary goal of a DoS attack is to disrupt the target service, making it inaccessible to legitimate users
- Financial losses: Downtime resulting from DoS attacks can lead to financial losses for businesses, particularly those that rely on continuous online operations
- Reputational damage: Extended service disruptions can tarnish an organization’s reputation, leading to loss of customer trust and loyalty
- Opportunities for other attacks: A successful DoS attack may serve as a distraction, providing an opportunity for other, more damaging cyberattacks
DDoS attacks and cloud environments
Cloud-based services are attractive targets for DDoS attacks due to their scalability and the potential to impact multiple customers hosted on the same infrastructure. DDoS attacks can be challenging to detect and mitigate in a cloud environment, as the traffic from multiple sources can be distributed and masked effectively.
DoS attack mitigation strategies
Let’s look at some examples:
- Traffic filtering: Implementing traffic filtering mechanisms can help block malicious traffic and allow only legitimate traffic to reach the target
- Rate limiting: Rate limiting restricts the number of requests from a single IP address, preventing an attacker from overwhelming the system with excessive requests
- Load balancing: Distributing traffic across multiple servers can help distribute the load and prevent one server from becoming overwhelmed
- Web Application Firewalls (WAFs): WAFs can identify and block malicious traffic targeting specific applications, helping protect against Layer 7 attacks
- Anomaly detection: Employing anomaly detection systems can help with identifying unusual traffic patterns and trigger proactive responses
The following figure depicts the WAF layout in the public cloud and shows how it interacts with AWS CloudFront:
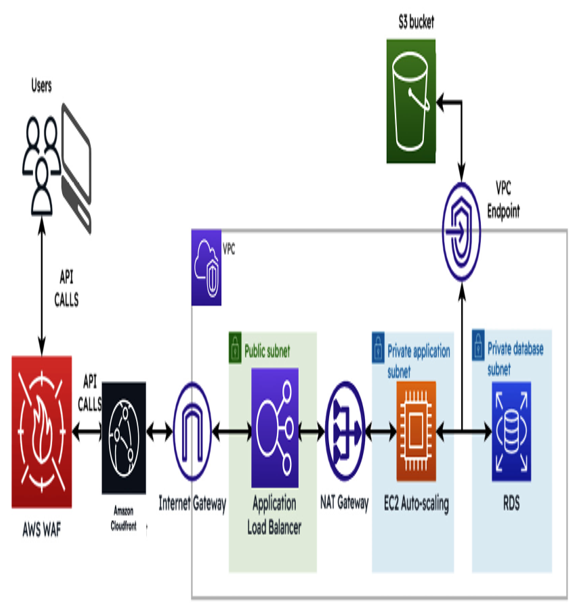
Figure 6.1 – WAF layout in AWS CloudFront
The preceding figure shows how the API calls interact with the AWS WAF service. Once they’ve gone through the WAF service, the API calls can interact with other AWS services. Please take note of the flow of the connection from the internet gateway to the application load balancer and then to other AWS services such as the EC2 instance.
Cloud-based DDoS protection services
Many cloud service providers offer DDoS protection services that leverage their distributed infrastructure to detect and mitigate DDoS attacks in real time. These services can effectively handle large-scale DDoS attacks and ensure minimal service disruption for customers.
Incident response and preparedness
Organizations must have a comprehensive incident response plan in place to detect and respond to DoS attacks promptly. Preparing for potential DoS attacks and conducting regular drills can improve the organization’s ability to respond effectively.
DoS attacks are a serious threat to the availability and stability of cloud-based services. Understanding the different types of DoS attacks and implementing appropriate mitigation strategies is crucial for organizations to protect their cloud environments from disruption. Cloud-based DDoS protection services and proactive incident response planning are essential elements of a robust defense against DoS attacks. By investing in proper defenses and staying vigilant, organizations can ensure the resilience of their cloud-based systems and maintain uninterrupted service availability for their users.